So first the NHS systems being locked down in England were reported, but it seems to be part of a global attack on several institutions.
Massive ransomware attack hits UK hospitals, Spanish banks
Massive ransomware attack hits UK hospitals, Spanish banks
TECHNOLOGY LAB —
Massive ransomware attack hits UK hospitals, Spanish banks
Ransomware attack appears to be targeting institutions in several European countries.
SEBASTIAN ANTHONY (UK) - 5/12/2017, 11:34 AM
Enlarge
Health Service Journal
82
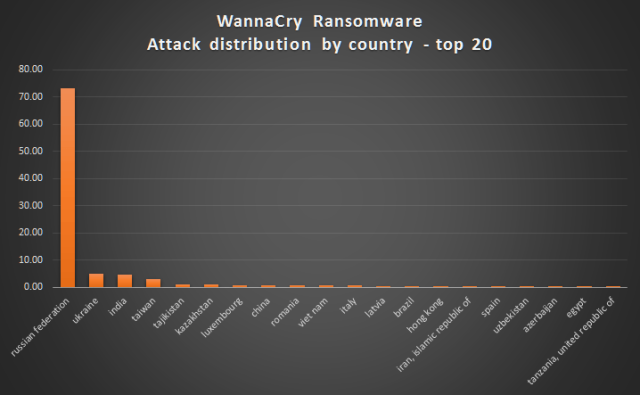
A large number of hospitals, GPs, and walk-in clinics across England have been locked down by a ransomware attack, reports suggest. There are also some reports of a ransomware attack hitting institutions in Portugal and Spain, with telecoms provider Telefonica apparently hit hard. Further attacks have been reported in Russia, Ukraine, and Taiwan. Batten down the hatches: we might be in the middle of a global ransomware attack.
Multiple sources point to this ransomware attack being based on the EternalBlue vulnerability, which was discovered by the NSA but was leaked by a group calling itself Shadow Brokers last month.
NHS Digital has confirmed the attack and issued a brief statement, stating that there's no evidence that patient data had been accessed and that the attack was not specifically targeted at the NHS. At this point it isn't clear whether a central NHS network has been knocked offline by the ransomware or whether individual computers connected to the network are being locked out. In any case, a number of hospitals and clinics are reporting that their computer systems are inaccessible, and some telephone services are down too.

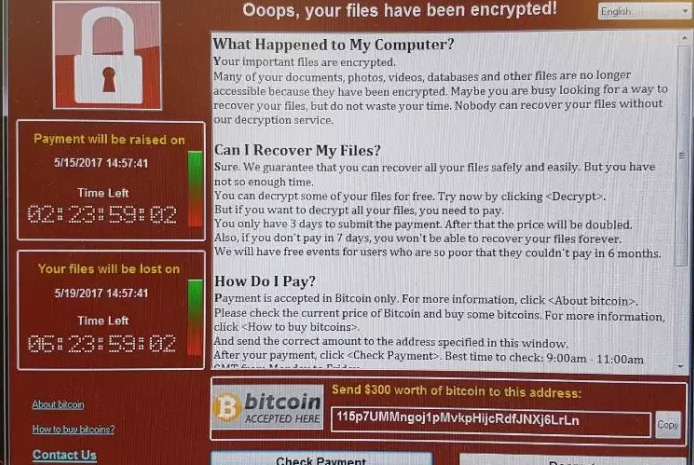
Enlarge / Another shot of the ransomware, this time obtained by the BBC. Note the slightly different timings on the left.
The Health Service Journal obtained a screenshot (pictured top) that purportedly shows the ransomware that is appearing on some NHS computers. At first glance it looks like your usual run-of-the-mill ransomware that demands $300 in bitcoin (about 0.16 BTC at today's exchange rate).
The Blackpool Gazette, which seems to have the most detailed report of the incident, has some pretty scary quotes from local hospitals and GP surgeries. The Blackpool Victoria Hospital has reportedly pleaded for patients to only attend A&E for life-threatening emergencies; "Please avoid contacting your GP practice unless absolutely necessary. Should you wish to obtain non-urgent medical advice please call 111," a spokesperson is quoted as saying.
Blackpool Gazette also spoke to a hospital IT worker who said that "five or six" NHS trusts had been taken offline by the malware. As of 15:30, NHS Digital said that 16 NHS organisations had reported being affected by the ransomware.
FURTHER READING
NHS trust battles mystery virus, turns away patients, shutters IT system"User shared drive access is down," the IT worker is quoted as saying. "E-mails slowly going. Non-essential PCs are being shut down, and waiting times are estimated to increase. There's nothing we can do except sit back and watch it collapse. The ransom message is exactly the same here, but with different bitcoin links, which is standard. It's a goodbye to the IT systems."
The East and North Hereford NHS Trust website shows the following message: "We're currently experiencing significant problems with our IT and telephone network, which we're trying to resolve as soon as possible. This means that people will have difficulty phoning us for the time being – please bear with us. Apologies for any inconvenience."
Foursys, an IT company, issued a statement saying 11 of its NHS customers have been affected by the ransomware.
Another screenshot of the ransomware shared by BBC Radio 5 Live shows the name "Wana Decrypt0r 2.0" in the title bar, which sounds very similar to Wanna Decryptor, a previously known piece of ransomware. The NHS Digital statement concurs: "The investigation is at an early stage, but we believe the malware variant is Wanna Decryptor."
FURTHER READING
Two more healthcare networks caught up in US outbreak of hospital ransomwareThe ransomware deadline appears to be at 3pm on May 19, exactly a week from now. We have reported on some isolated incidents of hospital ransomware in the past, both in the UK and the US, though the scale of this attack appears to be much larger than normal.
This story has been updated multiple times; we'll follow up with some technical analysis later today.
This post originated on Ars Technica UK